When Good Software Goes Bad
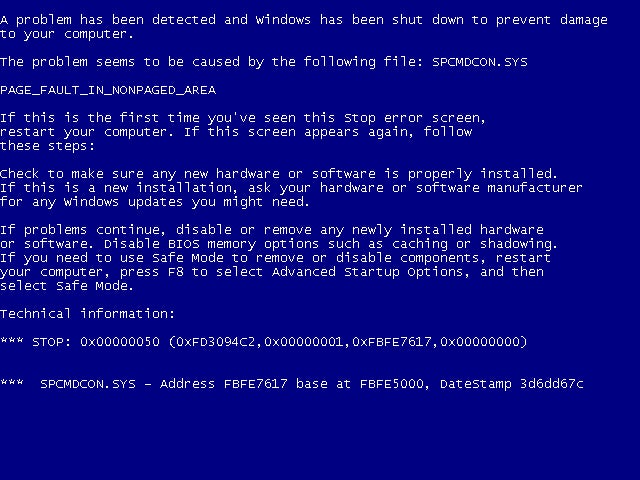
Buggy software is as annoying as it is a waste of both time and money. With more web-based software being downloaded into more devices every day — as opposed to native software dedicated to specific machines— the potential for stalls and diminished functionality grows. Additionally, bugs can leave devices vulnerable to security breaches. And, they’re just aggravating.
With a grant of nearly $500,000 from the National Science Foundation, UC Santa Barbara computer scientist Tevfik Bultan is looking for ways to improve and enhance our interactions with software. Bultan and his team are studying verification techniques that can catch and repair bugs in code that manipulates and updates data in web-based software applications.
“Developing software is still an error-prone process,” said Bultan. While the bigger companies are better able to hire talent to develop software with fewer bugs, in order to scale, the software development process should be viewed as an engineering problem as opposed to a matter of creativity and talent, he said, adding: “There’s a general lack of appreciation of how difficult it is to get the software right.”
The advantages of web-based software for users is its use of cloud-computing platforms to store information remotely in data centers. Not only can users access their programs from anywhere, at any time, their computers are less burdened by data-heavy software and can function with more agility.
However, with computing distributed across multiple machines on the cloud, errors and glitches are not easily detected before the software is rolled out to the public. As a result, bugs manifest themselves after the programs have been downloaded. This can cost a software company a lot in time, money and even user confidence. The problems people experience — and continue to experience — with the Healthcare.gov site, for example, illustrate the kind of frustration brought about by good software gone bad.
“It was used as a political discussion point, but not many people asked how come it failed from an engineering standpoint,” said Bultan.
Computer security is another huge area for bugs, with most issues traceable to an error in the program. The recent Heartbleed Bug, for instance, was a vulnerability in OpenSSL software, the very software that was used widely to encrypt communications over the Internet, compromising user names, passwords and other private information.
Using techniques that translate software data into code that can be evaluated with mathematical logic, Bultan’s team can verify the soundness of any particular software. By automating the process and adding steps to update the software as needed, crashes, perpetuated errors, vulnerabilities and other glitches will take up less time and money.
The verification can happen in various places in the process of developing software, he said, either before the program is rolled out to the public — static verification — or as a background process, as the software is being used. Bultan’s project, which concentrates specifically on web-based software, will emphasize static verification, although it will also include runtime checks.
The work also includes proposed guidelines for writing certain pieces of software code to allow for easier verification, and to avoid specific errors.
Still, with the complexity and diversity of software and new web-based applications continuously being developed, a solution to the problem of error-prone software may never be found. It’s mathematically impossible, according to Bultan, but this project takes a step toward approaching the issue from an engineer’s perspective, and eliminating the most common errors in software.
“We can’t catch all bugs, but we try to catch as many bugs as we can,” he said
Future projects might involve verification from the end user’s side, helping him or her write bug-free software.